What is WS_FTP Server? #
WS_FTP is a Progress Software (formerly ipswitch) product that allows customers to easily share files between teams and organizations. Progress Software describes WS_FTP as:
WS_FTP Professional is the safest and easiest way to securely upload and download files. Enjoy SFTP transfers with the highest levels of encryption, ease of use, customization, and low administrative overhead.
Latest WS_FTP Server vulnerability #
On September 27th, Progress Sofware announced eight vulnerabilities in the WS_FTP Server software. These issues can lead to a full compromise of exposed WS_FTP systems and their data through the FTP, SSH, and web management services, which are often externally exposed.
The four most serious vulnerabilities in this set:
-
CVE-2023-40044 (CVSS 10.0). An exposure in the web interface that leads to remote code execution through a .NET deserialization vulnerability. This is the issue most likely to be mass-exploited due to the lack of authentication and likelyhood of this web interface being exposed to untrusted networks. Rapid7 noted that this appears to be exploitable with a single HTTP POST request using an existing pauload from the ysoserial.net project.
-
CVE-2023-42657 (CVSS 9.0). An exposure in the FTP/SCP (SSH) implementation that enables file operations outside of the WS_FTP data folder through a directory traversal vulnerability. This issue can allow an attacker to access, modify, and delete files on the server, which can expose data, but also allow remote code execution in some configurations.
-
CVE-2023-40046 (CVSS 8.2). An exposure in the web interface that allows for database access through a SQL injection vulnerability. It's not clear if a valid user account is required to access this code path, but an attacker could use this to read and modify database contents, which in turn can lead to a full server compromise.
-
CVE-2023-40049 (CVSS 5.3). An exposure in the web interface that exposes file and directory lists within the WebServiceHost folder. Although this does not lead to remote code execution on it's own, it may be an important exposure in that it will help attackers identify systems vulnerable to the more serious issues above.
Are updates available? #
Progress Software has patched these issues in version 8.8.2.
How do I find potentially vulnerable versions of WS_FTP with runZero? #
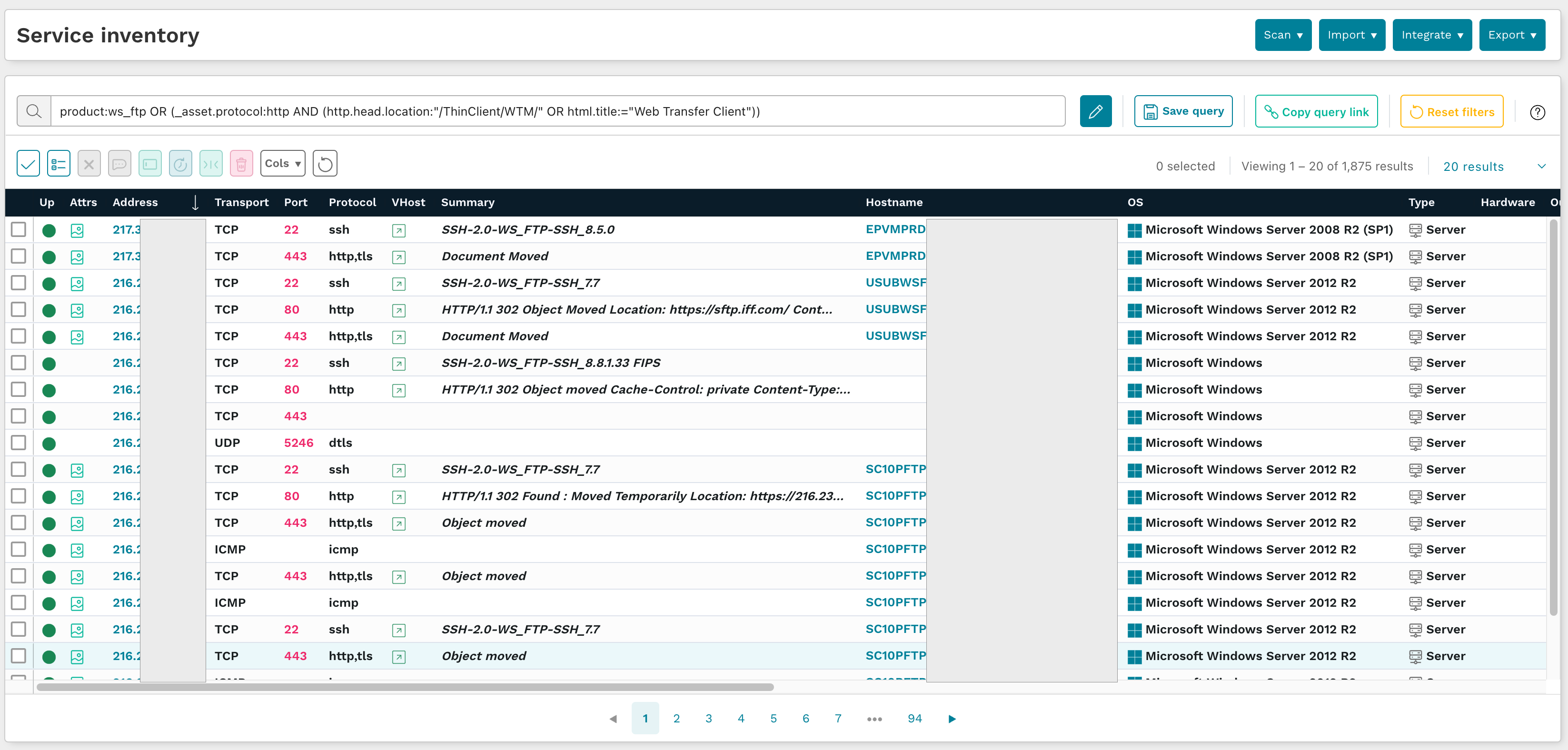
Assets with the WS_FTP FTP, SSH, and web services enabled can be found by navigating to the Service Inventory and using the following pre-built query:
product:ws_ftp OR (_asset.protocol:http AND (http.head.location:"/ThinClient/WTM/" OR html.title:="Web Transfer Client"))
To determine if the the instance has the WS_FTP Ad Hoc module installed, browse to
https://[instance-host:port]/AHT/AHT_UI/public/index.htmlIf the module is installed, this page will include an image like the one shown below:

If you are not using the Ad Hoc Transfer module, Progress Software has provided instructions for disabling it.
As always, any prebuilt queries are available from your runZero console. Check out the documentation for other useful inventory queries.
















